Introduction to Cyber Reconnaissance (Recon)

What is Reconnaissance?
Reconnaissance is the first phase of any attack. The goal of recon is to gather information regarding the target, weak points and defence system deployed.
The recon concept has been taken from the military aspect where they try to get information (recon) about the region of attack like terrain, count of enemies, type of weapons, etc. Once this is done, team can plan the execution strategy accordingly.
This can be applied to other aspects as well like sports. For example, in the game of cricket, bowler tries to recon about batting technique of the batsman and then plan the strategy for the same like bowling short ball to a specific batsman.
In the cyber world, attacker will try to gather information about digital assets like web application, network information, etc and defences deployed like firewall, etc.
Reconnaissance Types
There are two types of recon.
Passive Recon: In this recon, attacker tries to gather information without directly interacting with the target. Attacker uses publicly available information over the web typically refers to Open-source intelligence (OSINT).
Active Recon: In this attacker directly tries to connect with the target to find further information. Since attacker is directly interacting with the target here, there is a higher risk of self exposure.
Both the approaches has its own pros and cons. Passive is less riskier but active recon provide more information. They complement each other for gathering the information.
How to perform Reconnaissance?
In the below section we will look at two technique for recon. Although there are different tools available for the recon, we will try to build our own tools. We will be using python language to create the recon tool.
We will be using socket module of Python in the example. Below we will be talking about only limited information about socket. Please check the python docs for more details.
Socket is an endpoint which allows communication between two processes running on the same or different machine.
Below is the short code which can create a python socket.
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
socket.AF_INET represents the address family for ipv4 address family. This is a pair of (host, port). Other address family examples are AF_INET6, AF_UNIX.
socket.SOCK_STREAM defines it as TCP socket. Other general type is SOCK_DGRAM for UDP type.
The two recon techniques that we will be using are "Port Scanning" and "Whois" service.
Port Scanning (Active Recon)
In this technique, we will try to scan the open ports of the specific host.
Below is a simple script which can do the port scanning.
import socket
import sys
def main(ip, port_range='1-1024'):
# Create a tuple for start and end port
port_details = map(int, port_range.split('-'))
for port in range(*port_details):
# Create a socket of the AF_INET family which
# takes address of ipaddress and SOCK_STREAM defines
# TCP socket type
# For now just checking port open by creating a TCP connection
# but there will be other ways to check for the same too
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
# Try to connect to the given host and port
result = s.connect_ex((ip, port))
status = '\033[31mClose\033[m'
if result == 0:
status = '\033[32mOpen\033[m'
print('{0}: {1}'.format(port, status))
if __name__ == '__main__':
if len(sys.argv) < 2:
print('Invalid Arguments')
sys.exit(1)
port_range = '1-1024'
if len(sys.argv) == 3:
port_range = sys.argv[2]
main(sys.argv[1], port_range)
Now lets put the script into action.
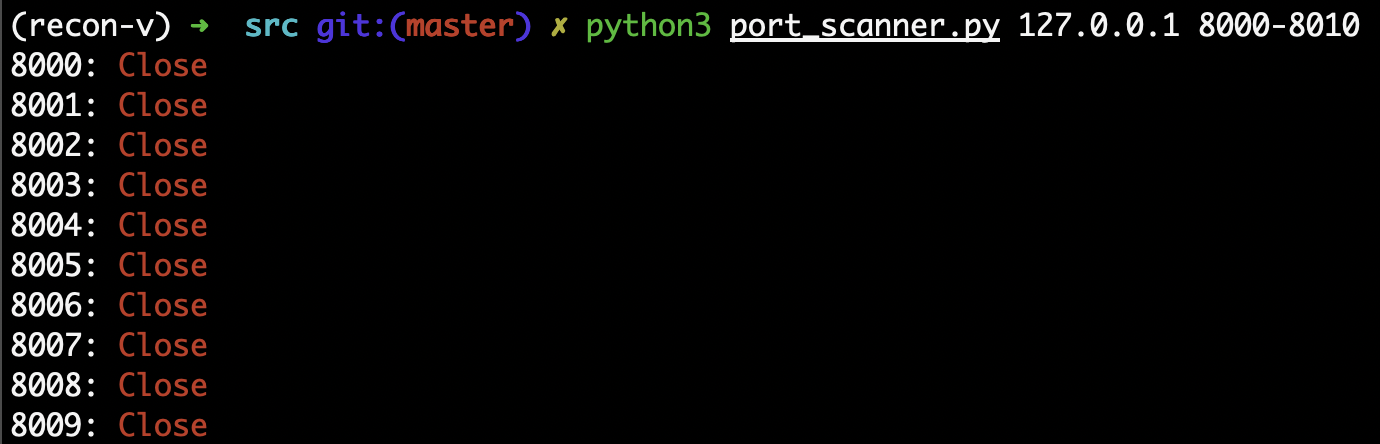
As we can see in the above sreenshot, I ran the script on my local instance with the port range of 8000 - 8010. Since there was no service running on those ports, so all the ports are shown as closed.
Now, lets start a simple python server on the port 8000. We can run the below command to start the server.
python3 -m http.server 8000
Lets run our port scanner again.
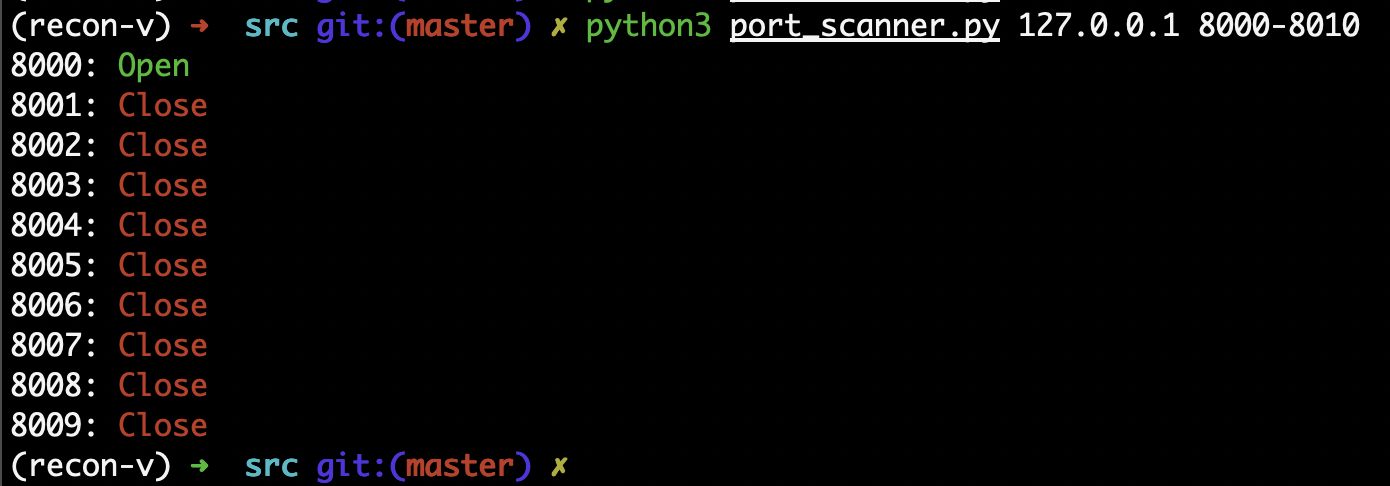
Now 8000 port is shown as open port since the python server is running on that port.
This way we can do a recon of the open ports on the host. We can further improve the script to take range of hosts as input as well.
Whois (Passive Recon)
Whois is a listing which provided details about the ownership of the domain.
Lets write a python script to provide info about whois details of a domain.
import socket
class SocketWrapper(object):
"""
A wrapper class to communicate with other socket
"""
def __init__(self, server, port=43):
self.server = server
self.port = port
def get_details(self, data):
# Creating a python socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
# Connecting to the server
s.connect((self.server, self.port))
data += '\r\n'
# Sending data to the server
s.send(data.encode())
message = ''
# Receiving data from server
while True:
return_data = s.recv(50000)
if not return_data:
break
message += return_data.decode('utf-8', 'ignore')
return message
def main():
domain = input('Enter Domain: ')
# https://raw.githubusercontent.com/whois-server-list/whois-server-list/master/whois-server-list.xml
# There are different servers responsible to provide the information for different domain.
# The above list can provide details about the responsible servers
domain_server = 'whois.verisign-grs.com'
#domain_server = 'whois.pir.org'
print(domain)
details = SocketWrapper(domain_server).get_details(domain)
print(details)
if __name__ == '__main__':
main()
Now we can run the above script and see how it works.
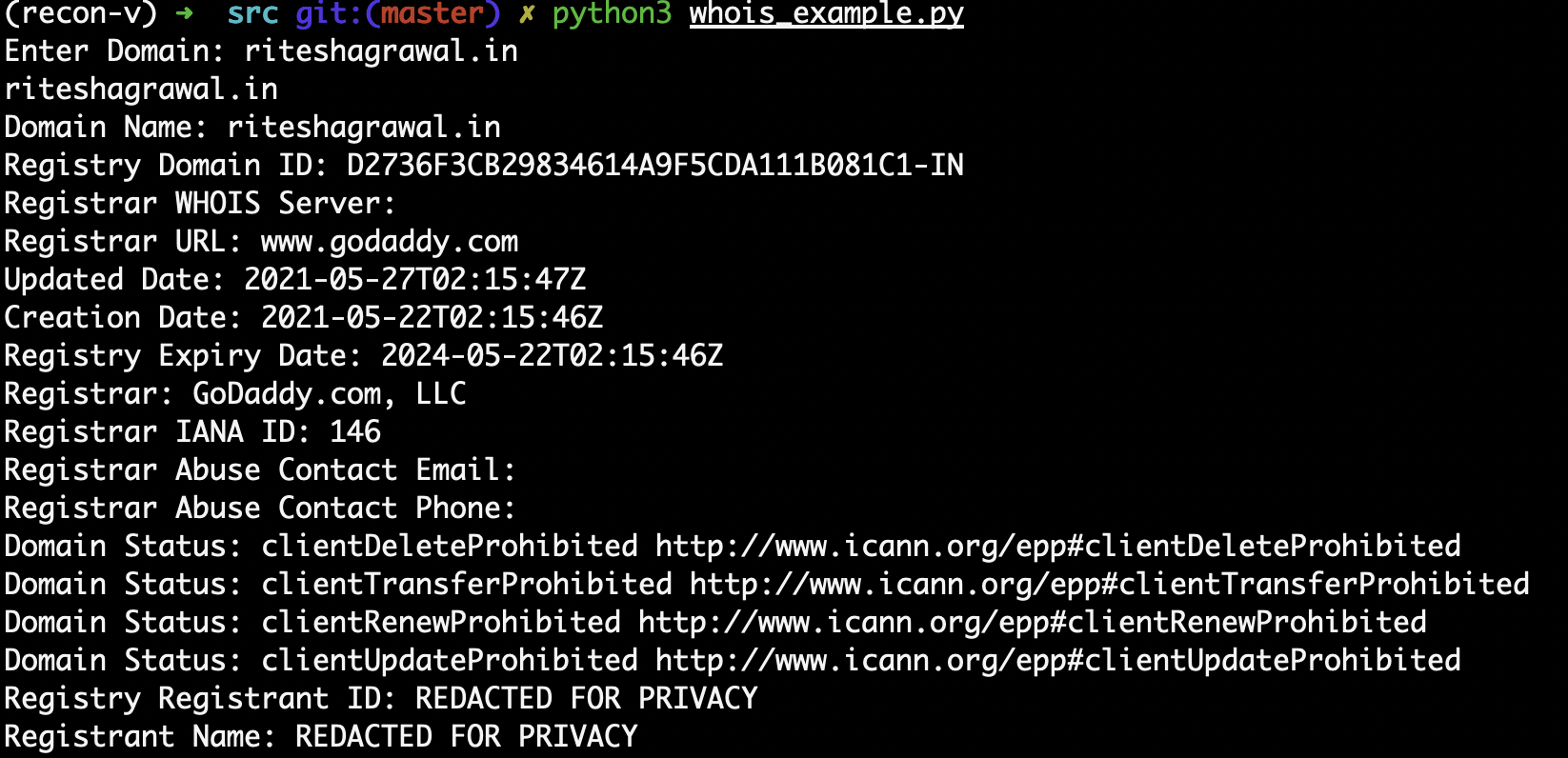
As we can see in the above screenshot, we can get details about riteshagrawal.in.
Conclusion
Cyber Reconnaissance is a very important phase of any attack. The information captured during this phase can help in preparation of effective strategy to be used for the attack.
